How Data Cyber Security Protects Your Organization from Emerging Threats
The Important Role of Data and Network Safety in Shielding Your Details
In an era where data violations and cyber dangers are increasingly widespread, the significance of robust information and network safety and security can not be overemphasized. The application of efficient safety and security actions, such as file encryption and access controls, is crucial to keeping count on and functional stability.
Recognizing Information Safety
In today's electronic landscape, an overwhelming bulk of organizations face the complexities of information safety and security. This essential element of info technology includes shielding sensitive information from unauthorized gain access to, corruption, or theft throughout its lifecycle. Information security incorporates various techniques and modern technologies, consisting of file encryption, gain access to controls, and data masking, all focused on guarding info against violations and vulnerabilities.
An essential element of data safety and security is the recognition and classification of data based upon its level of sensitivity and significance. This category aids companies prioritize their safety and security efforts, alloting sources to protect the most critical information efficiently. In addition, applying robust policies and procedures is important to ensure that employees recognize their duty in keeping information security.
Regular audits and analyses help in determining prospective weak points within an organization's data safety and security framework. Furthermore, worker training is crucial, as human mistake stays a considerable aspect in information breaches. By fostering a society of protection understanding, companies can reduce risks connected with expert hazards and neglect.
Value of Network Safety And Security
Network safety and security stands as a cornerstone of an organization's overall cybersecurity strategy, with about 90% of services experiencing some type of cyber threat in current years. The value of network safety and security depends on its capability to shield delicate info and maintain the honesty of company procedures. By securing network infrastructures, companies can avoid unauthorized access, information breaches, and various other harmful tasks that might jeopardize their possessions and track record.
Executing durable network security measures not only helps in mitigating threats however also promotes trust among stakeholders and clients. When customers are guaranteed that their personal and monetary details is protected, they are most likely to involve with the company, resulting in boosted customer commitment and business growth.
In addition, a well-structured network security structure promotes compliance with different regulatory demands. Organizations has to comply with market criteria and legal mandates worrying data security, and reliable network safety and security practices can ensure conformity, consequently avoiding prospective charges.

Common Cyber Threats
Organizations have to continue to be attentive versus a range of cyber dangers that can undermine their network safety and security efforts. Amongst the most common threats is malware, which incorporates infections, worms, and ransomware that can interrupt operations, take information, or hold info hostage. Phishing strikes, where destructive stars impersonate relied on entities to deceive individuals right into disclosing delicate info, continue to expand in refinement, making user education and learning vital.
Another common threat is distributed denial-of-service (DDoS) strikes, which overload systems with traffic, making them unavailable to genuine customers. Expert risks, whether willful or unintentional, present significant risks as staff members may unintentionally reveal delicate data or intentionally exploit their accessibility for destructive functions.
In addition, susceptabilities in software and hardware can be made use of by cybercriminals, highlighting the value of normal updates and spot monitoring. Social engineering strategies even more make complex the landscape, as aggressors adjust people right into disclosing secret information through psychological manipulation.
As these risks progress, companies need to maintain an aggressive technique to identify, reduce, and respond efficiently to the ever-changing cyber danger landscape, securing their important info and maintaining trust fund with stakeholders. fft pipeline protection.
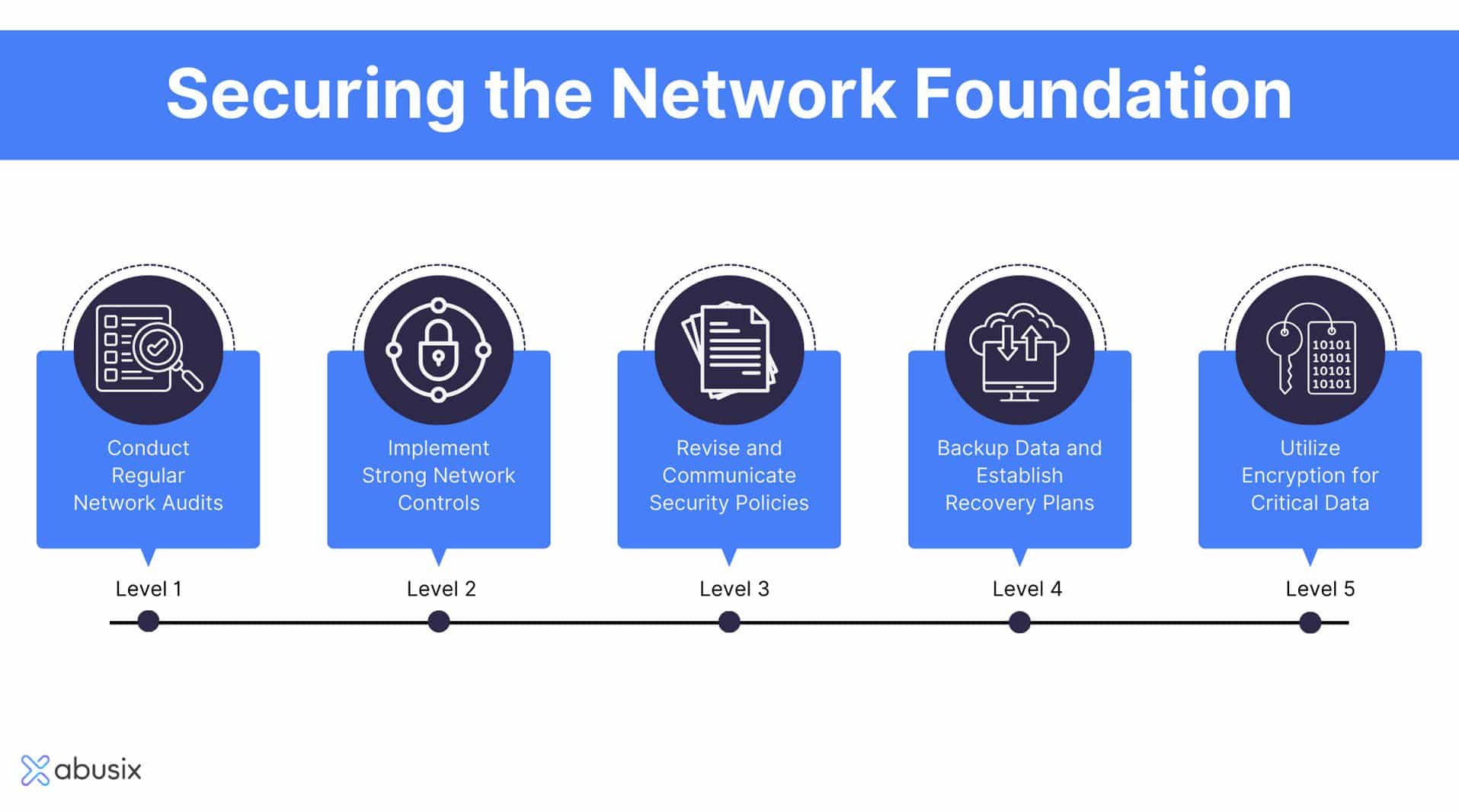
Ideal Practices for Defense
Carrying out robust security actions is important for safeguarding sensitive information and keeping functional integrity. Organizations needs to start by carrying out comprehensive danger evaluations to identify susceptabilities within their systems. This aggressive strategy makes it possible for the prioritization of safety efforts tailored to the details demands of the organization.
Adopting solid password policies is vital; passwords ought to be complex, frequently changed, and took care of utilizing secure password monitoring tools. Multi-factor verification (MFA) adds an added layer of safety by requiring added verification techniques, thus reducing the threat of unapproved accessibility.
Normal software program updates and spot management are crucial to secure against understood vulnerabilities. Carrying out firewalls and invasion discovery systems can even more secure networks from external dangers. Employee training is similarly crucial; team ought to be enlightened on recognizing phishing attempts and recognizing the importance of data protection protocols.
Data file encryption need to be used for delicate information, both at rest and in transit, to guarantee that even if data is intercepted, it stays unattainable (fft pipeline protection). Last but not least, companies should establish and on a regular basis examination occurrence feedback intends to make certain speedy activity in the occasion of a security breach. By sticking to these finest practices, organizations can improve their safety position and safeguard their vital data assets
Future Trends in Protection
The landscape of information and network safety is constantly developing, driven by advancements in technology and the increasing class of cyber risks. As organizations increasingly take on cloud computing and IoT devices, the standard of safety and security will change toward a zero-trust version. This technique highlights that no entity-- interior or external-- is naturally trusted, mandating confirmation at every gain access to point.
In addition, making use of expert system and artificial intelligence in protection procedures gets on the increase. These modern technologies allow anticipating analytics, enabling companies to determine susceptabilities and potential next threats prior to they can be exploited. Automation will likely play a pivotal function in simplifying safety responses, minimizing the moment taken to alleviate breaches.
In addition, regulatory structures will certainly remain to tighten up, necessitating extra rigid Go Here conformity steps. Organizations has to stay abreast of progressing regulations to ensure they fulfill security requirements.
Conclusion
Finally, the value of data and network security can not be overemphasized in the contemporary electronic landscape. With the occurrence of cyber risks and the raising intricacy of regulatory needs, organizations should embrace comprehensive protection procedures to protect delicate information. By remaining and executing reliable methods educated regarding emerging fads, companies can boost their durability versus potential assaults, ensuring data honesty and fostering depend on amongst stakeholders and customers. Prioritizing safety and security continues to be necessary for functional continuity and lasting success.
In an age where information breaches and cyber risks are significantly widespread, the importance of robust information and network security can not be overstated. Information protection includes various techniques and innovations, including file encryption, accessibility controls, and information masking, all intended at safeguarding info versus violations and susceptabilities.
A basic facet of information security is the identification and category of information based on its level of sensitivity and importance.The landscape of data and network security content is continually developing, driven by improvements in innovation and the raising sophistication of cyber hazards.In verdict, the value of information and network protection can not be overemphasized in the modern electronic landscape.